Master Paul Vines
UW CSE Security and Privacy PhD student Paul Vines defended his quals project today, the key research milestone for receiving his Masters degree in Computer Science & Engineering. Great job Paul!
Paul G. Allen School of Computer Science & Engineering, University of Washington
UW CSE Security and Privacy PhD student Paul Vines defended his quals project today, the key research milestone for receiving his Masters degree in Computer Science & Engineering. Great job Paul!
UW Security and Privacy lab researcher Temitope Oluwafemi publishes an invited article in The Conversation about computer security and the Internet of Things.
Check out the article here: https://theconversation.com/can-a-hacker-stop-your-car-or-your-heart-security-and-the-internet-of-things-33273
In an article entitled, “Tacoma Police Change How They Seek Permission to Use Cellphone Tracker,” The News Tribune quotes UW CSE’s Ian Smith. Quoting from the article:
“Ian Smith is a security researcher in the University of Washington Computer Science & Engineering Security and Privacy Lab and has studied cell site simulators and similar devices.
“… Cellphone companies have the ability to access that kind of information now, Smith said. Cell site simulators give that capability to anyone who knows how to use them, including the police, he said.”
Read more here: http://www.thenewstribune.com/2014/11/15/3488642_tacoma-police-change-how-they.html?rh=1
Congratulations Dr. Karl Koscher for a very successful final defense! UCSD is very fortunate to be having you join their team!
 UW CSE Professor Yoshi Kohno was invited to run Session 1 at the Stanford Cybersecurity Bootcamp for U.S. Congressional Staffers. The session focused on threat modeling and developing the security mindset.
UW CSE Professor Yoshi Kohno was invited to run Session 1 at the Stanford Cybersecurity Bootcamp for U.S. Congressional Staffers. The session focused on threat modeling and developing the security mindset.
 The EFF just released a new online privacy tool, called Privacy Badger, to help protect against third-party tracking on the web.
The EFF just released a new online privacy tool, called Privacy Badger, to help protect against third-party tracking on the web.
The EFF worked with Franzi Roesner to integrate her ShareMeNot functionality into Privacy Badger. Privacy Badger uses the ShareMeNot techniques to handle social media widgets.
To quote from the EFF Press Release: “EFF wishes to thank Professor Franziska Roesner at the University of Washington for exceptional work in enhancing Privacy Badger’s widget-handling algorithms.”
UW CSE Security Lab’s Karl Koscher is featured on German TV. See Karl’s interview starting around minute 6. Great job Karl! The video also includes clips of UW CSE Security Lab members and alumni Alexei Czeskis, Tadayoshi Kohno, and Franzi Roesner. Read more about the UW CSE automotive security effort, in collaboration with UCSD, here.
 Congratulations to Roxana Geambasu for winning a highly coveted Microsoft Research Faculty Fellowship!! This is a very high honor! Roxana is a Columbia University professor and past UW CSE PhD student. To quote from the Microsoft web page: “Each year since 2005, Microsoft Research has recognized innovative, promising new faculty members from a number of research institutions to join the ranks of Microsoft Research Faculty Fellows.” And: “We are pleased to announce the 2014 Faculty Fellows, seven young professors from the following five regions: Latin America and the Caribbean; Europe, the Middle East, and Africa; the United States and Canada; Australia and New Zealand; and Korea, Hong Kong, Taiwan, and Singapore.” Congratulations Roxana!
Congratulations to Roxana Geambasu for winning a highly coveted Microsoft Research Faculty Fellowship!! This is a very high honor! Roxana is a Columbia University professor and past UW CSE PhD student. To quote from the Microsoft web page: “Each year since 2005, Microsoft Research has recognized innovative, promising new faculty members from a number of research institutions to join the ranks of Microsoft Research Faculty Fellows.” And: “We are pleased to announce the 2014 Faculty Fellows, seven young professors from the following five regions: Latin America and the Caribbean; Europe, the Middle East, and Africa; the United States and Canada; Australia and New Zealand; and Korea, Hong Kong, Taiwan, and Singapore.” Congratulations Roxana!
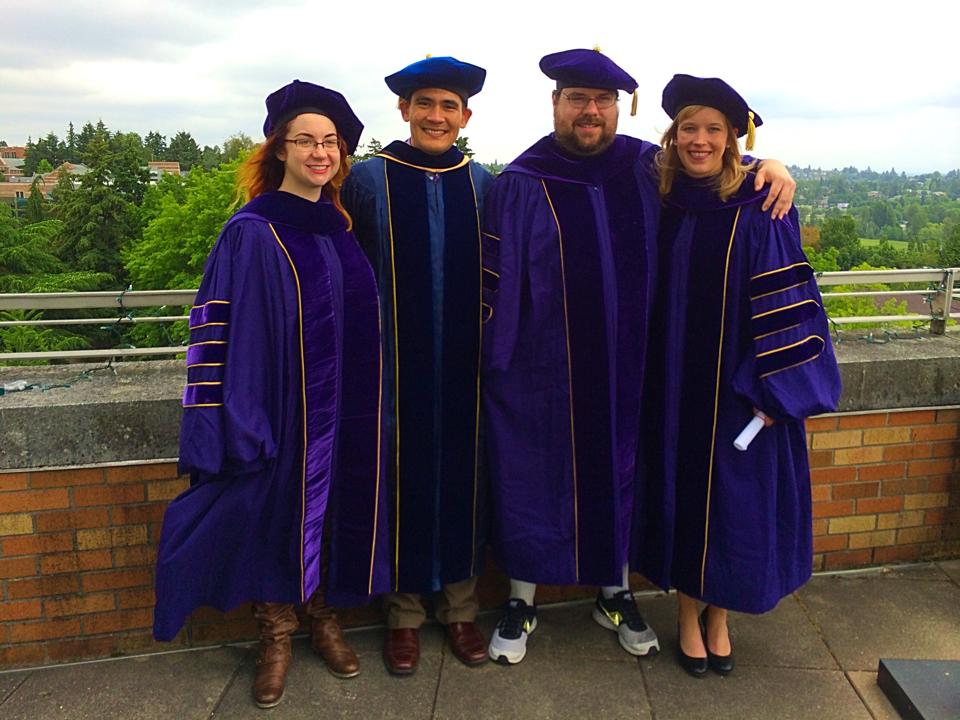 Congratulations to Franzi, Karl, and Tammy for walking today as part of your PhD graduations! We are very proud of all the UW CSE graduates!
Congratulations to Franzi, Karl, and Tammy for walking today as part of your PhD graduations! We are very proud of all the UW CSE graduates!
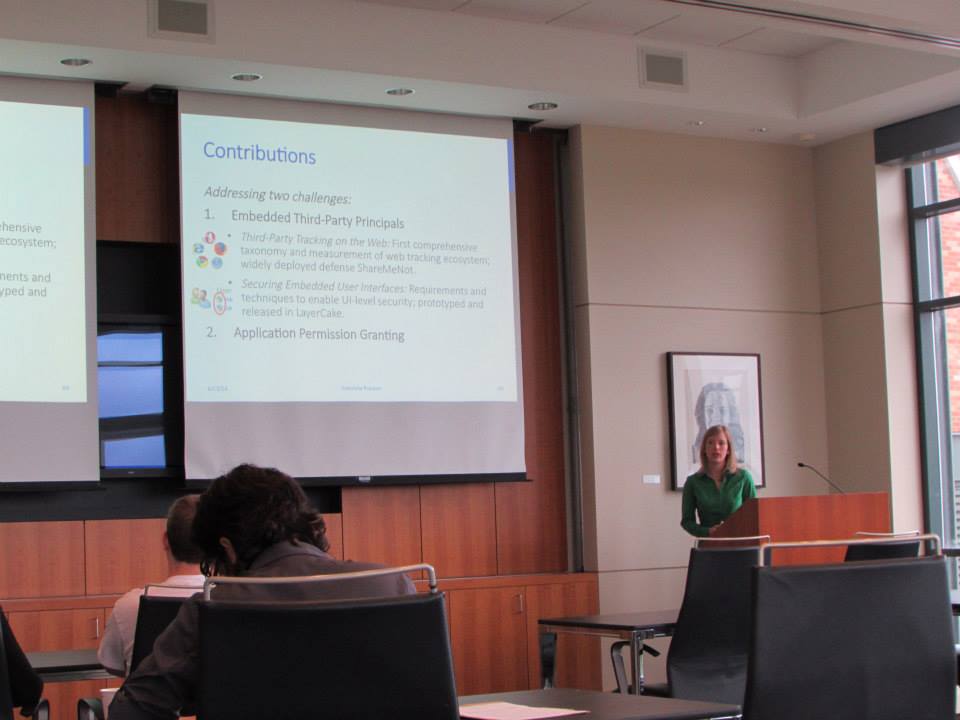 Congratulations Prof. Dr. Franzi Roesner for a very successful final defense!
Congratulations Prof. Dr. Franzi Roesner for a very successful final defense!